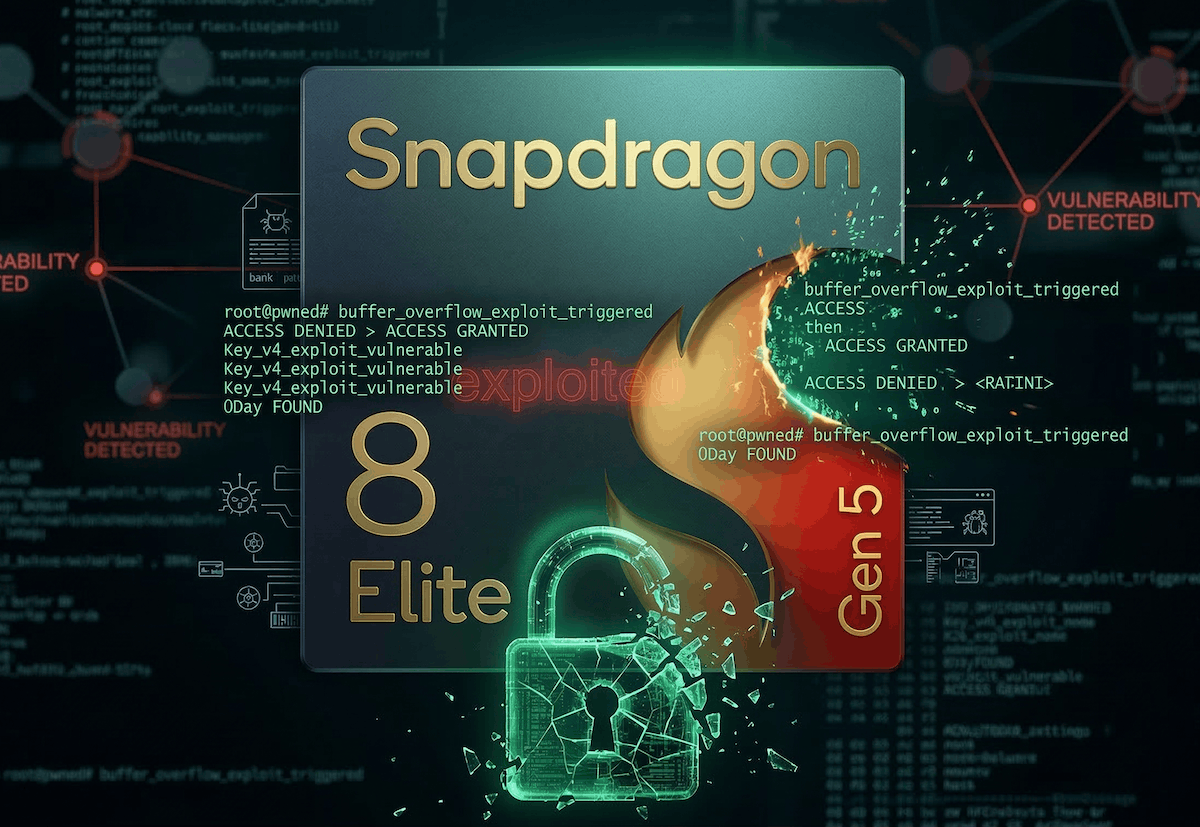
You know what has always set Android apart from iOS? Freedom. Custom ROMs, root access, full control over your device — for enthusiasts, this is a matter of principle. And now, while we were busy with other things, the community literally exploded — an exploit appeared online that allows unlocking the bootloader on flagships with the latest Snapdragon 8 Elite Gen 5. Xiaomi 17, Redmi K90 Pro Max, POCO F8 Ultra — phones that were considered impenetrable suddenly turned out to be open to any attacker. But Qualcomm has already responded and confirmed that patches have been sent to manufacturers. Let’s figure out whether you should worry and what’s actually going on.
If you have a current 2025 flagship, it’s better to update your software.
What Is the Qualcomm Exploit and How Does It Work
The essence of the exploit lies in how the Qualcomm bootloader (ABL) handles loading certain components. On devices running Android 16, the bootloader loads these components in a special partition but only checks for the presence of a UEFI application — not its authenticity. You can slip in unsigned code, and the bootloader will execute it. Honestly, it sounds like a hole the size of a truck.
But you can’t just write something to the partition — special mechanisms block such actions. To switch it to executable mode, you need root. And to get root, you need to unlock the bootloader. A classic “chicken and egg” problem.
And this is where the second vulnerability comes into play. ABL accepts a command that should only accept 0 or 1, but in practice doesn’t filter input arguments at all. This allows adding a separate parameter and switching the system with a single command. And it actually works.
Unlocking the Xiaomi 17 Bootloader Through an Exploit Chain
On Xiaomi smartphones, the chain turned out to be even more interesting. To write a custom UEFI application to the efisp partition, researchers exploited a vulnerability in the MQSAS app — a proprietary Hyper OS service with system privileges. This is how they obtained the necessary write permissions.

You have to choose: freedom to use your smartphone or the risk of it being hacked.
After rebooting, the bootloader picks up the substituted UEFI application without any verification — thanks to the base GBL vulnerability. The custom application sets the activation value to 1 — doing exactly the same thing as the manufacturer’s standard command. Just without their permission.
Xiaomi, as a reminder, has significantly complicated the unlocking procedure in the Chinese market — questionnaires, timers, device restrictions. Most users simply gave up on it. And now — a workaround has been found. However, Xiaomi may have already patched the vulnerability in Hyper OS 3.0.304.0 builds.
Which Snapdragon Smartphones Are Affected by the Vulnerability
Successful unlocking has been confirmed for Xiaomi 17, Xiaomi 17 Ultra, Redmi K90 Pro Max, and POCO F8 Ultra — all running Snapdragon 8 Elite Gen 5. But the base GBL vulnerability apparently affects all devices with Qualcomm chips running Android 16. The exception is Samsung with its own S-Boot bootloader.
Theoretically, the OnePlus 15 and other 2026 flagships are also at risk. However, the exploit chain for each brand will differ — the second part of the vulnerability on OnePlus or Realme devices may look different. Or may not exist at all. The GBL exploit can’t be called a universal solution — but as a starting point, it looks quite serious.
Should You Update Your Snapdragon 8 Elite Gen 5 Smartphone
Qualcomm didn’t stay silent. A company representative confirmed that fixes were sent to manufacturers back in early March 2026. The research was conducted by the Xiaomi ShadowBlade Security Lab team — Qualcomm praised them for responsible disclosure of the vulnerability.

Updating your smartphone, as always, solves many security problems.
Qualcomm recommends installing security updates as soon as possible. That’s sound advice. But here’s the paradox: the updates that close the vulnerability also close the loophole for bootloader unlocking. If you wanted to install a custom ROM on your Xiaomi 17 — you shouldn’t update just yet. But in that case, you’ll have to live with the vulnerabilities.
And so we’ve arrived at the question that divides the Android community into two camps. Qualcomm has sent patches to manufacturers, and sooner or later updates will arrive on all affected devices. But until the patches are rolled out — users have a window of opportunity.
Everyone has to decide for themselves. If security is important to you — update at the first opportunity. A bootloader vulnerability is no joke. But if you’ve been waiting a long time for the chance to unlock the bootloader and are ready to take responsibility, you can take the risk. The main thing is to understand the risks. They can’t be called very large, but they exist.
The situation is ambiguous. For Qualcomm — it’s a vulnerability that needs to be patched. For users — it’s a rare opportunity to regain control over their device. But one thing is certain — the question of Android modification freedom hasn’t gone anywhere and concerns a huge number of people.