A toolkit for hacking iPhones called DarkSword has been published in open access on GitHub. Yes, the very same one that is the reason you need to urgently update your iPhone to the latest iOS — and this is no joke. According to researchers, even a person without specialized knowledge could use it — and hundreds of millions of Apple devices running outdated versions of iOS are now at risk. Apple has already released updates, but far from everyone has installed them.

The virus that can hack an iPhone is now available to anyone. A very troubling precedent. Image: 9to5mac.com
What Is DarkSword and How Does It Hack iPhones
DarkSword is a set of six vulnerabilities that are used in a chain to gain full control over an iPhone or iPad. The attack begins through the Safari browser: simply opening an infected or spoofed web page is enough to compromise the device. No confirmation from the user is required — this is a so-called drive-by attack, where infection occurs simply by visiting a website.
After penetrating through Safari, the malicious code sequentially bypasses several layers of iOS protection and ultimately gains full access to data: contacts, photos, passwords, messages, crypto wallets, and files. Researchers from Google, iVerify, and Lookout previously detected DarkSword being used in targeted attacks in Saudi Arabia, Turkey, Malaysia, and Ukraine — by both government hackers and commercial spyware vendors.
Why the DarkSword Leak on GitHub Is a Serious Problem
Previously, DarkSword was used by isolated groups with significant resources. Now the code has been posted on GitHub — the largest developer platform, owned by Microsoft. iVerify co-founder Matthias Frielingsdorf stated directly to TechCrunch:
This is bad. They are too easy to repurpose. I don’t think this can be contained. You should expect criminals to start using this.
According to him, the files on GitHub are simple HTML and JavaScript that can be copied and launched on one’s own server within minutes or hours. No deep knowledge of iOS is required. One security researcher already demonstrated that they were able to hack an iPad mini running iOS 18 using the leaked sample. Google confirmed this assessment.
Which iPhones and iPads Are at Risk from DarkSword
The vulnerabilities exploited by DarkSword affect devices running iOS versions from 18.4 to 18.7. Older versions of iOS — 15 and 16 — are also vulnerable, for which Apple separately released patches.

Security updates are available even for iPhone 6s — it’s important to install them
If your iPhone or iPad is running one of these versions and hasn’t been updated, it’s at risk:
- iOS 18.4–18.7 (before updating to 18.7.3 or iOS 26.2)
- iOS 16 (before updating to 16.7.15)
- iOS 15 (before updating to 15.8.7)
This applies to a wide range of models — from iPhone 6s and the first-generation iPhone SE to current models that simply weren’t updated in time. According to Apple, this could involve hundreds of millions of active devices worldwide. And according to StatCounter data, by the beginning of 2026, only about 15–16% of iPhone users had switched to iOS 26 — the rest are running older versions.
How to Protect Your iPhone from DarkSword
The main protection is updating iOS to the latest available version. Apple emphasized: devices with up-to-date software are not susceptible to these attacks. Here’s what you need to do:
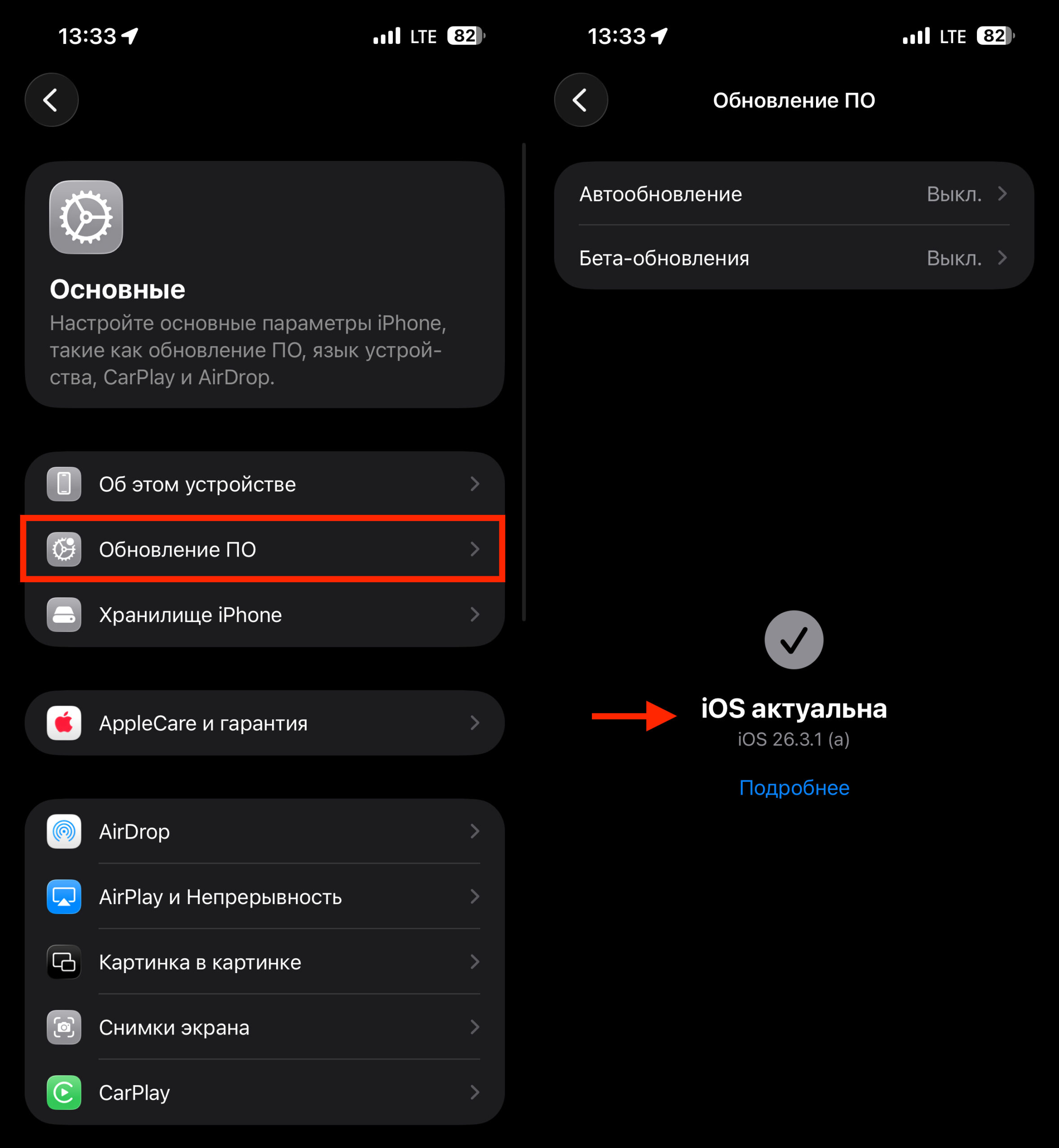
Make sure you have no pending iOS updates
- Open Settings → General → Software Update
- If an update is available — install it. For older devices this is iOS 16.7.15 or iOS 15.8.7, for newer ones — iOS 26.3 or iOS 18.7.3
- Connect to Wi-Fi and make sure the battery level is at least 50% (or plug in the charger)
The size of updates for older devices is about 100–200 MB, and downloading and installing will take just a few minutes.
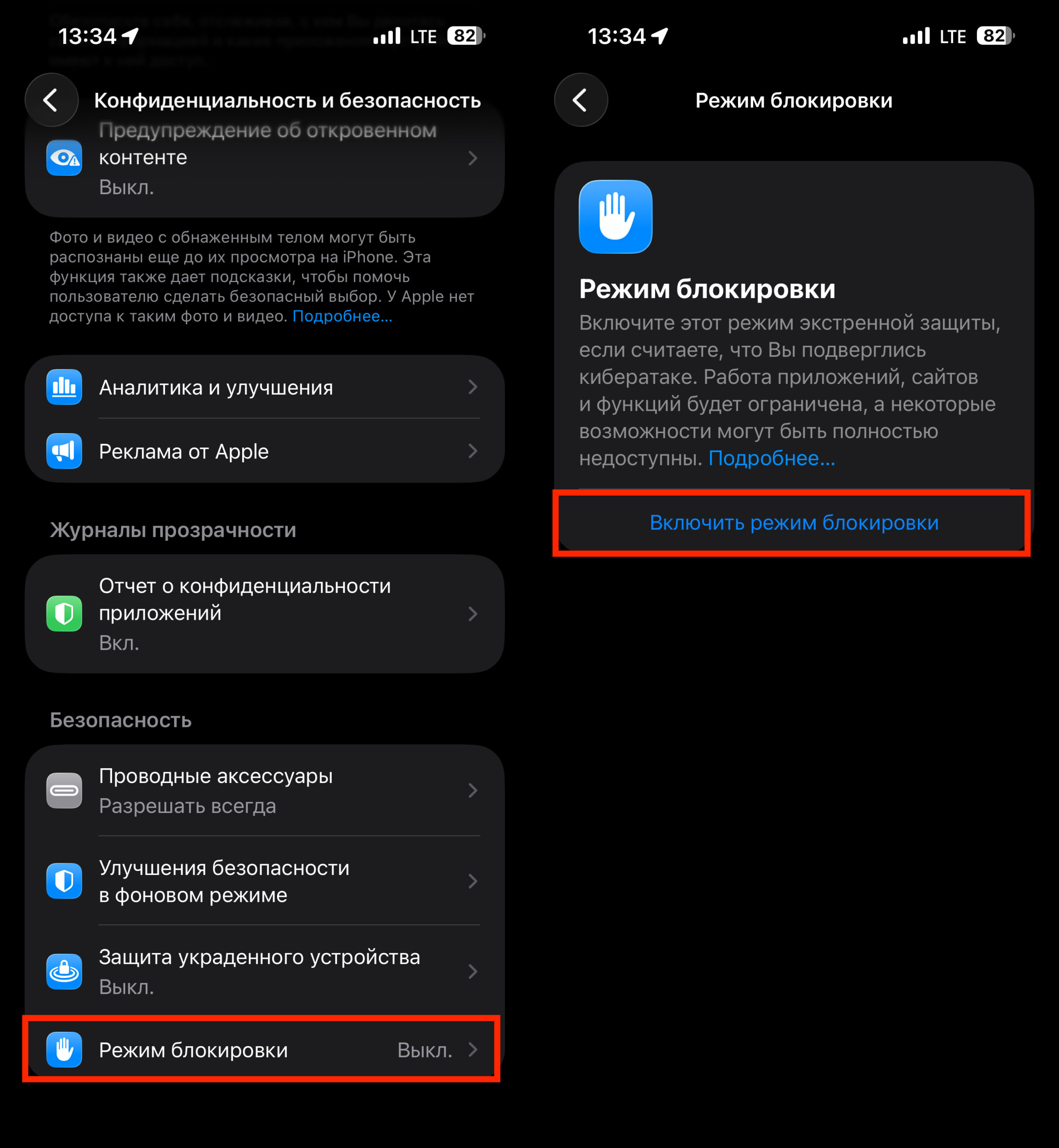
If needed, you can enable Lockdown Mode
An additional measure is Lockdown Mode. Apple confirmed that it also blocks DarkSword attacks. Lockdown Mode disables some Safari features (including the very web technologies through which the exploit works), restricts attachments in Messages, and blocks incoming FaceTime calls from unknown contacts. You can enable it in Settings → Privacy & Security → Lockdown Mode. The mode is available on iPhone 8 and newer (with iOS 16+). For everyday use it’s excessive and inconvenient — but if for some reason you can’t update, it’s a reasonable temporary measure.
Apple spokesperson Sarah O’Rourke confirmed that the company was aware of the exploit and released an emergency update on March 11 for devices that cannot run the latest versions of iOS. According to her:
Keeping your software up to date is the most important thing you can do for the security of your Apple devices.
She also added that Lockdown Mode is effective against these specific attacks. Microsoft, which owns GitHub, did not comment on the situation at the time of publication and did not say whether removal of the code from the platform is planned.
How Dangerous Is DarkSword for the Average iPhone Owner
If your iPhone is updated to the latest available version of iOS — there’s no reason to panic. All vulnerabilities used by DarkSword have already been patched by Apple. The problem concerns those who postpone updates or use an older device running iOS 15, 16, or 18 without the latest patches.
Special attention should be paid by owners of iPhone 6s, 7, 8, X, and first-generation SE — these models are still popular on the secondary market and actively used. They won’t receive iOS 26, but security updates iOS 15.8.7 and 16.7.15 are available for them, which close exactly these vulnerabilities. If you or your loved ones have such an iPhone — check the iOS version right now. This is perhaps one of those cases when an update truly cannot be postponed.